Just about all companies collect data, including many you work with. Your business too collects data from customers to aid in its operations. In terms of your own privacy, though, you should take certain measures to protect your personal data. Here are some of the ways you can combat the predatory practices of advertisers and cybercriminals alike.
(415) 246-0101
Microtechs Blog
There has been a good deal of controversy about how personal data has been collected, sold, and used over the past few years. Companies of all types package and sell data to create a valuable extra revenue stream for their business, and while this should be thought of as a side effect of all the data that is created by people, it can also create some pretty difficult situations to try and navigate. Today, we’ll take a look at the data-broker loophole, how it works, and what can be done about it.
A lot of people don’t take cybersecurity and data privacy seriously enough, and that puts both them and others at risk. We’ve all gotten used to sharing personal information online—whether it’s on social media, shopping websites, or other digital services. But if we’re not careful, this can lead to big problems like hackers stealing your identity or money. When people don’t use strong passwords or turn on two-factor authentication, they leave gaps that hackers can take advantage of. These gaps don’t just affect individuals—they can lead to bigger cyberattacks that hurt entire organizations or communities.
Cybersecurity tops the list for any business’ needs, particularly when one considers just how many threats are out there today. This makes it essential that today’s businesses (yours included) put an assortment of cybersecurity tools and protections in place.
We’ve assembled a list of the ones we recommend.
Technology continues to play a major role in healthcare, especially as it has become more prominent. Through technology, the healthcare industry has been able to stabilize costs, improve access, and personalize care delivery—challenging concepts in years past. That said, these innovations come at the cost of potential issues with data privacy… issues that become more prominent as technology becomes even more advanced.
Personally identifiable information—or PII—is critically important data for individuals and businesses, not only because operations rely on many of these data points but there are also significant circumstances for losing it. Of course, to properly protect PII, you need to know what the umbrella term of PII includes.
Let’s talk a little bit about deepfakes. If you aren’t aware of this technology, deepfakes are essentially synthetic media. Typically they come in the form of videos or images that use artificial intelligence (AI) to replace a person’s likeness with another’s. With deepfake technology, people can convince an audience that a person said something they didn’t say. This deliberate digital subterfuge can bring with it a whole lot of problems. This week we will outline a few of them.
Data privacy has never been such an important issue for businesses and individuals alike. In some places, calls for overarching legislation to protect consumers have often been met with significant pushback by lawmakers who are reluctant to put extra regulations on businesses, while others have passed important laws dictating how organizations handle individual data.
We know that security is far from a small investment, but this only serves to highlight how important it can be to your business’ continued success. You might wonder why security is such an important investment if you don’t intend to suffer a data breach, and that’s precisely the point. The cost of not investing in security far outweighs the initial investment.
We bet you’ve gone through your old files at some point to clean things up a bit by deleting files from your computer. What if we told you that deleting those files doesn’t actually delete them—at least not entirely? Let’s go over how you can securely delete your files for good while you go about replacing hardware or upgrading your technology systems.
For years you’ve heard how technology is becoming a bigger part of the healthcare delivery system and how it can help stabilize costs, provide increased access, and further personalize care delivery. As these innovations have been taking hold it has brought up serious questions about data privacy. Today, we’ll take a look at some of the changes IT has brought to healthcare and what it means for patient data privacy.
Privacy for business means a lot more than protecting the data and personal information of clients. It also extends to just about all data collected by a business, including that of the employees. How can you go about protecting this data without also violating the privacy of your employees themselves?
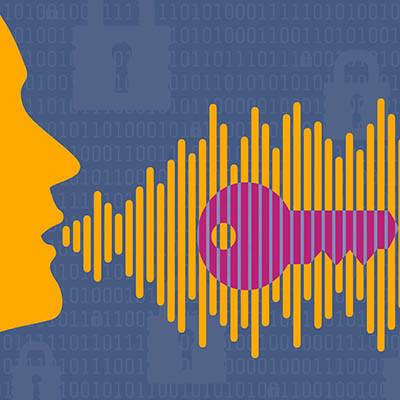
With so many workers performing tasks remotely, it’s no small wonder that authentication is one of the major points of discussion this year. How can you be sure that your company is doing all it can to verify a user’s identity before they access important information on your infrastructure? One such way you can do it is by using voice-based authentication.
When it comes to network security, there is a lot that can go wrong for your business and countless solutions that you can implement to combat them. However, there are small practices that you can implement on a daily basis to improve security as a whole, so if your collective staff can implement this one easy trick, you might be surprised by how beneficial it can be for your network’s security. This practice? Locking your computer.
Data privacy is central to most conversations in the business environment, and in a time when ransomware and hacks of all kinds are constantly receiving media presence, it’s no surprise that it is sensationalized to a certain extent. That said, it’s critical for businesses to understand what needs to be done to future-proof their data privacy infrastructures.